SSL¶
SSL (Secure Socket Layer) ensures confidentiality and integrity of data transmission, as well as server and sometimes client authentication. It is based on asymmetric encryption and X.509 certificates. On serv00.com servers, SSL configuration is performed using the DevilWEB administration panel and the devil ssl command.
SNI¶
On serv00.com servers it is possible to use your own certificate in a traditional way with your own previously purchased private IP address or without it using the SNI technology. However, please note that SNI is not compatible with all older browsers.
Generating free Let's Encrypt certificates¶
We provide full, automatic support for free Let's Encrypt certificates, including their renewals. Generating Let's Encrypt certificates is possible with both the DevilWEB panel and the devil command.
Warning
When generating, the Let's Encrypt organization checks for domain A records on external DNS servers. The domain must point to the web IP address (default address) or private address purchased by the user.
DevilWEB¶
In order to generate and add a Let's Encrypt certificate via the DevilWEB panel, after logging in to the panel go to SSL ➡ WWW websites ➡ Manage (with the selected IP address) ➡ + Add certificate ➡ select Generate Let's Encrypt certificate from the list.
Devil¶
To generate and add a Let's Encrypt certificate using the Devil tool execute the command: devil ssl www add IP_ADDRESS le le DOMAIN_NAME where:
- IP_ADDRESS - is the IP address at which the website is available
- DOMAIN_NAME - is the domain of the website
CSR¶
The CSR (Certificate Signing Request) file is necessary to place an order and issue an SSL certificate.
To generate the CSR file log in to your account and then use the command: openssl req -new -nodes -sha256 -newkey rsa:2048 -out req.pem -keyout cert.key. The req.pem file generated in this way should be sent to the company that will provide the certificate. The cert.key file is needed on the server side. It should be stored safely and not made available to third parties. If you lose it you will not be able to install the certificate.
Intermediate certificates¶
Each browser has its own database of trusted certificate issuers. The new issuer generates an intermediate certificate instead of waiting for the update of such a database. In order for the issued certificate to work it must be combined into one file (SSL certificate chains). The supplier should inform about the sequence of their connection. The intermediate certificate must be linked to the certificate for the domain.
Linux
To combine intermediate certificates execute command: cat domain.crt bundle1.crt bundle2.crt bundle3.crt (...) > domain.chained.crt (domain.chained.crt is the result of the command - a combined certificate).
Windows
To connect the certificate with intermediate certificates, create a new text file and paste the contents of the file with the certificate and intermediate certificates into it (the order of intermediate certificates according to information from the certificate issuer). Save the new text file under any name, preferably adding the .crt extension at the end.
DevilWEB¶
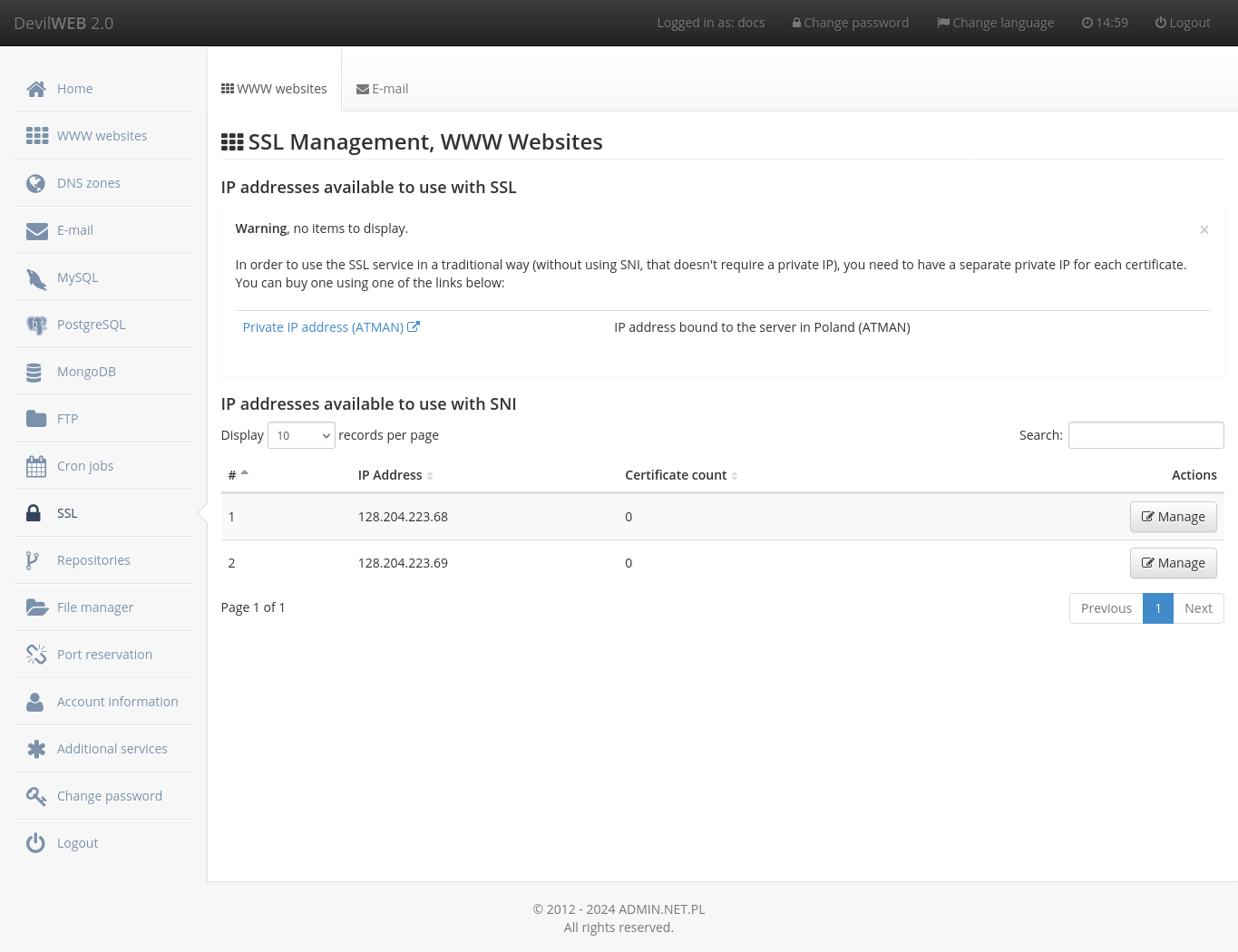
After logging in to the administration panel you can manage the SSL certificates in the SSL tab. The WWW certificate management can be found in theWWW websites tab. If you do not have your own IP address, you can use the SNI option. The management of e-mail certificates can be found in the E-mail tab. After clicking the 'Manage' button, a list of certificates for that address will be displayed next to the IP address. To add a certificate, go to the + Add certificate tab. Select the certificate file, key file and domain name for which the certificate was issued.
Devil¶
Adding and removing a web certificate¶
Adding a certificate to a website is done with the command devil ssl www add IP_ADDRESS CERTIFICATE KEY [DOMAIN_NAME], where the arguments are:
- IP_ADDRESS - private IP address of the user or web server when using SNI
- CERTIFICATE - path to the file with the certificate
- KEY - path to the SSL key file not protected with a password
- [DOMAIN_NAME] - domain name to be configured with SNI (optional)
Removing the WWW certificate is done with the command devil ssl www del IP_ADDRESS [DOMAIN_NAME]
List of WWW certificates¶
The list of certificates is available with the command devil ssl www list.
Adding and removing a certificate for mail¶
Adding a certificate for mail is done with the command devil ssl mail add IP_ADDRESS KEY CERTIFICATE, where the arguments are:
- IP_ADDRESS - private IP address of the user
- CERTIFICATE - path to the file with the certificate
- KEY - path to the SSL key file not protected with a password
Removing the mail certificate is done with the command devil ssl mail del IP_ADDRESS
List of certificates for mail¶
The mail certificate list is available with the command devil ssl mail list.
Downloading SSL certificates¶
It is possible to download SSL certificates with the keys from our configuration, including the Let's Encrypt certificates generated using our system.
DevilWEB¶
The certificate download option is available in:
- For web certificates:
SSL➡WWW Websites➡Manage➡Download - For mail certificates:
SSL➡Mail➡Manage➡Download
Devil¶
Syntax of commands for downloading certificates:
- For WWW certificates:
devil ssl www get IP_ADDRESS [DOMAIN_NAME] - For mail certificates:
devil ssl mail get IP_ADDRESS
Converting the certificate from DER to PEM format¶
The conversion of the certificate from the binary DER format to the PEM format supported by our system can be done with the command:
openssl x509 -inform der -in FILENAME_IN_DER_FORMAT.cer -out RESULT_PEM_FILE.crt
Check that the results of the following commands are identical:
openssl x509 -in RESULT_PEM_FILE.crt -pubkey -noout -outform pem | sha256sum
and
openssl pkey -in PRIVATE_KEY.pem -pubout -outform pem | sha256sum